ClawJacked, Axios, and the Autonomous Agent Problem
- Haggai Philip Zagury
- Agentic ai , Dev ops
- April 10, 2026
Table of Contents
TLDR; In a single 72-hour stretch of March 2026, we watched three independent attack surfaces on autonomous agents fail at once: OpenClaw’s localhost gateway (ClawJacked), the Axios npm package (a cross-platform RAT), and Anthropic’s own Claude Code source map leak — all converging on March 31. I’m not a security expert. I’m a DevOps practitioner who ran the homework before running the software, and this post is that homework. Part 1 is the problem. Part 2 will be what I’d want to be true before I run a personal assistant in a form of agent.
A Note Before We Start
I am not a security researcher. I don’t live on security mailing lists or CVE (Common Vulnerabilities and Exposures) feeds. I have colleagues who do, and I consult them before I run anything new. Then I do my own research, which is how this post came to exist. If you’re a security professional and I’ve flattened a nuance, please correct me — the link to every source is at the bottom, and I’d rather be corrected than confidently wrong.
With that disclaimer on the table: the last six weeks in agentic AI security have been bad enough that I think every DevOps and platform engineer needs to understand what happened, even if security isn’t your primary beat.
The 72 Hours That Should Worry You
Let me set the scene with a timeline, because the timeline is the story.
February 26, 2026 — Oasis Security discloses ClawJacked, a vulnerability chain in OpenClaw (formerly Moltbot/Clawdbot) that lets any website silently take over a developer’s locally-running AI agent. No plugin. No browser extension. No user interaction. Just visit a webpage.
March 18–21, 2026 — Nine OpenClaw CVEs drop in four days, including a 9.9 critical that turns any authenticated user into admin via a single WebSocket message. Sandbox escape, approval wrapper bypass, allowlist bypass via shell line-continuation — the entire “human in the loop” safety story, which was OpenClaw’s core marketing claim, had fundamental implementation gaps.
March 31, 2026 — Two things happen on the same day. First, a North Korean threat actor (Sapphire Sleet / UNC1069) publishes backdoored versions of the Axios npm package, delivering a cross-platform RAT (WAVESHAPER.V2) to macOS, Windows, and Linux. Axios sees around 100 million weekly downloads. The malicious versions are live for roughly three hours; SANS estimates 600,000 installs in that window. Second, Anthropic accidentally ships a JavaScript source map for Claude Code v2.1.88 to npm, exposing ~513,000 lines of unobfuscated TypeScript. Within hours, it’s mirrored, forked, and weaponized into malware droppers posing as “leaked Claude Code.”
Zscaler called the overlap “a perfect storm for anyone updating Claude Code via npm that day.” That’s the line I can’t stop thinking about. If you ran npm install during that window, with an autonomous agent watching your terminal, you had three attack surfaces lit up simultaneously.
What ClawJacked Actually Was
Let’s zoom in on ClawJacked, because it’s the cleanest example of why autonomous agents are different.
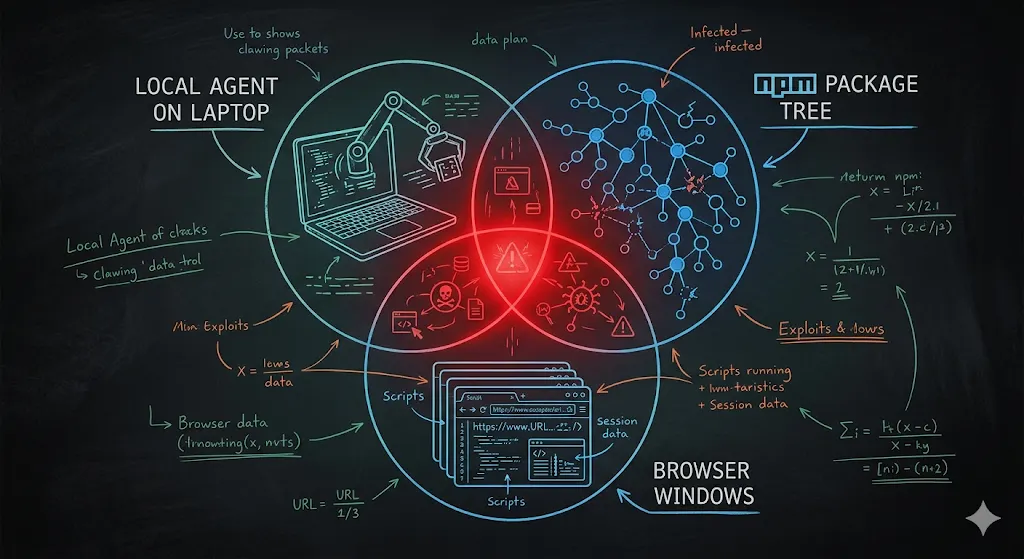
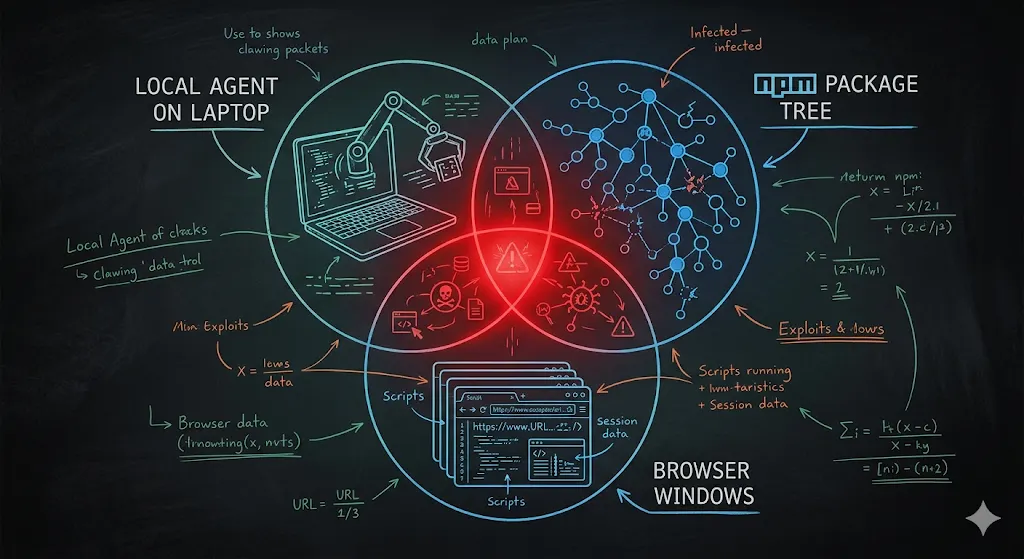
OpenClaw runs a local gateway — a WebSocket server bound to localhost, protected by a password. The reasoning is straightforward: only local tools should talk to it, so loopback connections get relaxed security. No rate limit. Failed auth attempts aren’t logged. New device pairings from localhost get auto-approved.
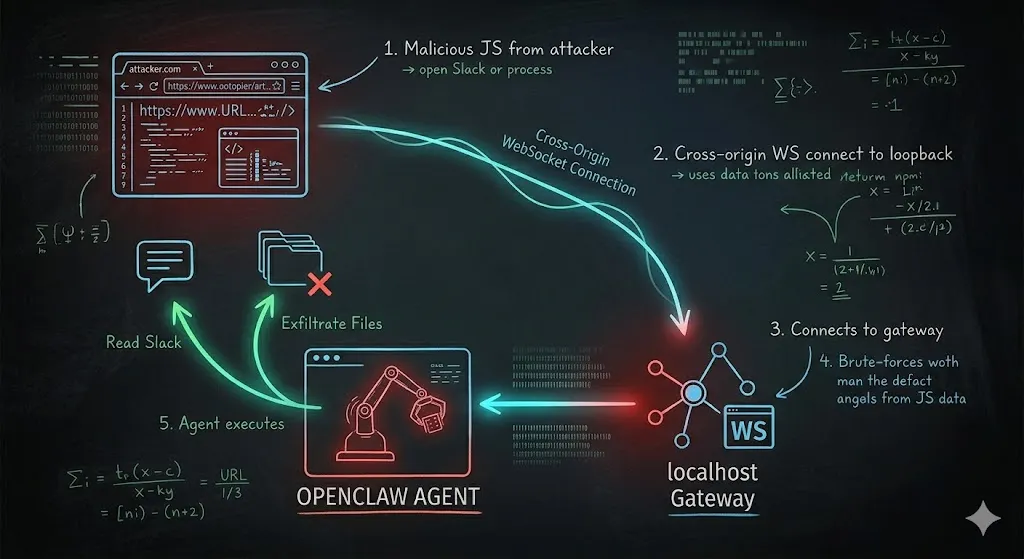
Here’s the problem Oasis found: browsers don’t block cross-origin WebSocket connections to localhost. So any website you visit — any website — can have JavaScript that opens a socket to your local OpenClaw gateway. From the gateway’s perspective, it’s a local connection. From your perspective, you just opened a tab.
Once connected, the attacker brute-forces the password. Oasis measured sustained rates of hundreds of guesses per second from browser JavaScript alone. Common password lists fall in under a second. With the password, the attacker registers as a trusted device (auto-approved, remember?), then instructs the agent to do what agents do: read Slack history for API keys, exfiltrate files, execute shell commands on any paired node.
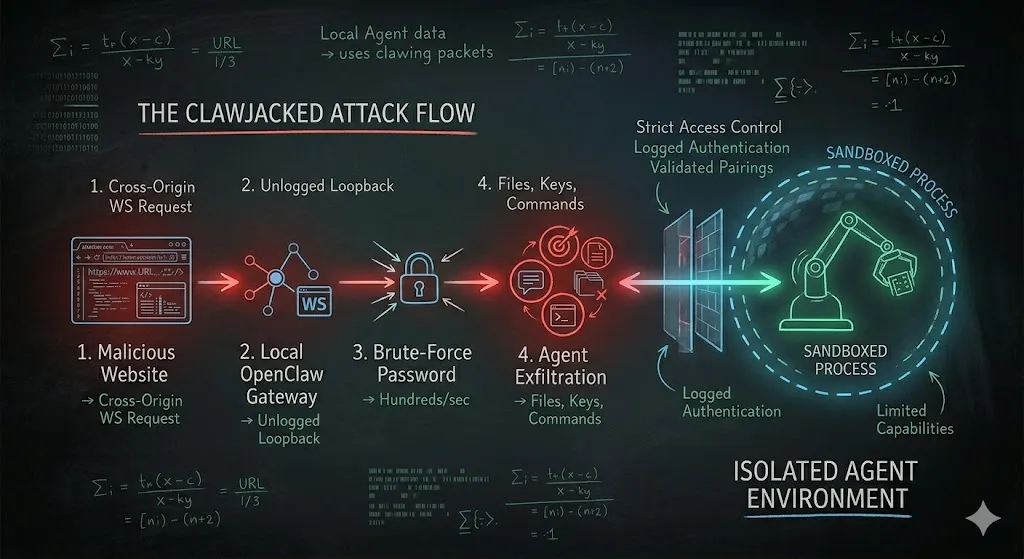
OpenClaw patched it in under 24 hours. That response time is admirable. It also isn’t the point. The point is that an assumption we’ve carried for decades — localhost is trusted — broke the moment we started running autonomous agents behind it. 🤔🤔🤔
The Ecosystem Rot Around the Core
ClawJacked was the cleanest bug, but not the only one. In parallel, researchers found over 1,000 malicious skills on ClawHub (OpenClaw’s plugin marketplace) — fake crypto tools and productivity integrations that actually deployed info-stealers. Bitsight and NeuralTrust documented 42,900+ internet-exposed OpenClaw instances, with 15,200 vulnerable to RCE (Remote Code Execution**)** at various points. The March CVE flood included a sandbox inheritance bug (CVE-2026–32048), meaning even sandboxed agents could escape, and an “allow always” wrapper bypass (CVE-2026–29607) where approving a safe-looking wrapped command once let attackers swap the inner payload later without re-prompting.
Read that again. The approval you gave yesterday covered commands you didn’t intend. The human-in-the-loop model — the thing that was supposed to make agents safe — had holes big enough that old approvals became new attack vectors.
And this is all happening to a project that hit 100,000 GitHub stars in five days. That growth curve is also part of the story.
Why Agents Make Supply Chain Attacks Worse
Now let’s stack Axios on top.
Axios is an HTTP client. You’ve probably never typed npm install axios directly — it’s a transitive dependency in thousands of packages. On March 31, a compromised maintainer account published versions 1.14.1 and 0.30.4 with a phantom dependency ([email protected]) whose postinstall hook deployed a platform-specific RAT. Huntress observed the RAT (Remote Access Trojan) beaconing every 60 seconds, enumerating filesystems, accepting remote commands.
This is a classic supply chain attack. It would have been bad regardless of AI. But here’s what autonomous agents change: the agent is the blast radius amplifier.
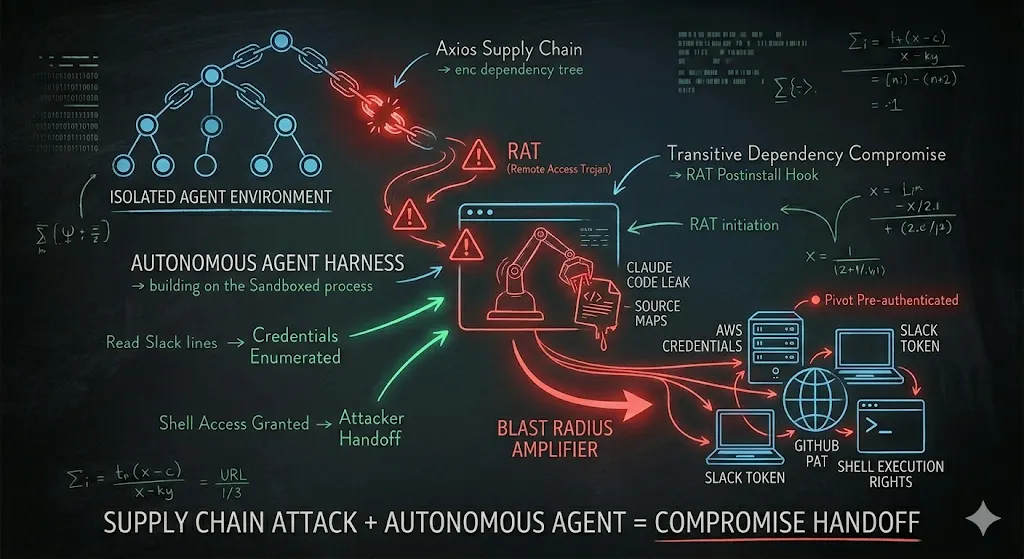
A traditional developer workstation compromise is bad. A developer workstation compromise where the agent holds your Slack token, your AWS credentials, your GitHub PAT, has shell execution rights, and is already authorized to take actions on your behalf — that’s not a compromise, that’s a handoff. The attacker doesn’t need to figure out how to pivot. The agent is the pivot, pre-authenticated, pre-authorized, patiently waiting for the next instruction. 😮😮😮
And Axios isn’t an isolated incident. Team PCP hit Trivy and LiteLLM earlier in March. That’s two different threat actors, one DPRK-affiliated and one English-speaking, independently proving the same playbook works. SANS’s Josh Wright called supply chain compromise “too rich an opportunity for attackers to ignore.” Five days later, Axios happened.
While all this unfolded, Claude Code had its own bad quarter — Check Point-disclosed vulnerabilities in configuration file handling in February, then the March 31 source map leak that dropped the entire internal agent harness into the public, giving attackers a roadmap for future exploits. I’m mentioning this not to single out any one vendor, but to make the opposite point: even the teams with the most resources and the deepest security practice are struggling with the autonomous agent attack surface. This is hard for everyone, especially myself which uses agent’s for almost anything …
Lets not Blame the Messenger …
Here’s where I want to be careful. It would be easy to read this post as “OpenClaw bad, don’t use it.” — That’s not my argument.
The OpenClaw maintainers patched ClawJacked in under 24 hours after responsible disclosure. That’s a better response time than most enterprise vendors manage. The project is volunteer-driven, transparent about its vulnerabilities, and actively hardening.
If you Google “openclaw hosting,” you’ll already find a handful of providers offering managed instances — the commercial ecosystem is racing ahead of the security model, but that’s not the hosting providers’ fault either. They’re selling hardware or IaaS — as they always have …
The problem isn’t any single project or provider. The problem is the category. A self-hosted, always-on process with:
- A local network surface (the gateway)
- A large dependency tree (supply chain surface)
- Shell execution rights (privilege surface)
- Stored credentials for your SaaS tools (identity surface)
- An LLM that reads external content (prompt injection surface — we’ll cover this in Part 2)
These all serve as a combination lock where any one dial turning unlocks the whole machine. In March 2026, every single dial turned. Some of them turned twice.
What I’d Want You To Know Before Deciding
I’m not telling you to rip out your agents. I’m telling you to understand what you signed up for. If you’re running an autonomous agent on your laptop or a V.P.S right now, here’s the honest version of what you’re maintaining:
- You are running an always-on service that needs patch hygiene at the speed of upstream disclosure. Nine CVEs in four days means you’re doing security updates as a weekly activity, not a “set and forget” install.
- You are trusting your entire dependency tree, including dependencies you never chose, to never have a bad day. Axios had a bad day. So did Trivy. So did LiteLLM.
- You are assuming the “human in the loop” approval model holds — despite March 2026 showing us two separate ways it didn’t.
- You are granting the agent the union of every credential it has access to, and treating that union as a single blast radius.
That’s not an argument against agents. It’s an argument for clear-eyed choices.
I want a personal agent. I want it badly enough that I’ve been testing alternatives — nanobot, nanoclaw, agent-sandbox as a containment pattern — which I’ll cover in Part 2. But I’m not running one pointed at my real credentials yet, and after March 2026, I don’t think you should either, unless you’ve made a deliberate decision about each of the surfaces above.
In the next post, I’ll walk through what I’m testing, what a sandboxed agent architecture could look like, why prompt injection is the attack you can’t patch with a CVE, and the pre-flight checklist I’d want to clear before I trust any agent with the keys to my digital life.
See you there.
Further Reading
- Oasis Security — ClawJacked: OpenClaw Vulnerability Enables Full Agent Takeover
- OpenClawAI blog — Nine CVEs in Four Days: Inside OpenClaw’s March 2026 Vulnerability Flood
- jgamblin — OpenClawCVEs tracker
- Microsoft Security Blog — Mitigating the Axios npm supply chain compromise
- Huntress — Supply Chain Compromise of axios npm Package
- Elastic Security Labs — Inside the Axios supply chain compromise
- Wiz — Trivy compromised in TeamPCP supply chain attack
- LiteLLM — Security update March 2026
- Zscaler ThreatLabz — Anthropic Claude Code Leak
- SecurityWeek — Claude Code Flaws Exposed Developer Devices to Silent Hacking
- Mashable — What is MoltBot, the viral social media AI agent and the frightening OpenClaw vulnerability