ClawJacked, Axios, and the Autonomous Agent Problem
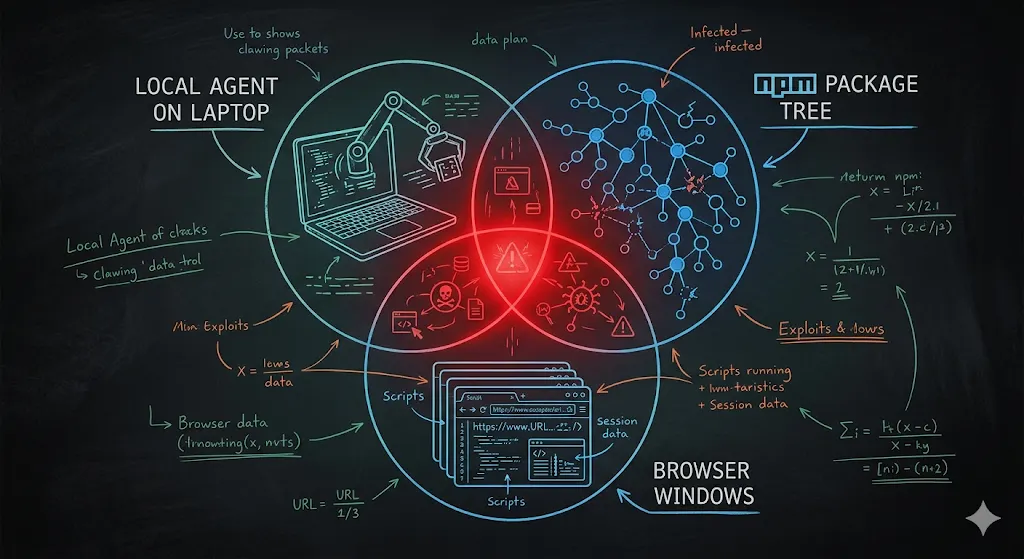
TLDR; In a single 72-hour stretch of March 2026, we watched three independent attack surfaces on autonomous agents fail at once: OpenClaw’s localhost gateway (ClawJacked), the Axios npm package (a cross-platform RAT), and Anthropic’s own Claude Code source map leak — all converging on March 31. I’m not a security expert. I’m a DevOps practitioner who ran the homework before running the software, and this post is that homework. Part 1 is the problem. Part 2 will be what I’d want to be true before I run a personal assistant in a form of agent.
Read More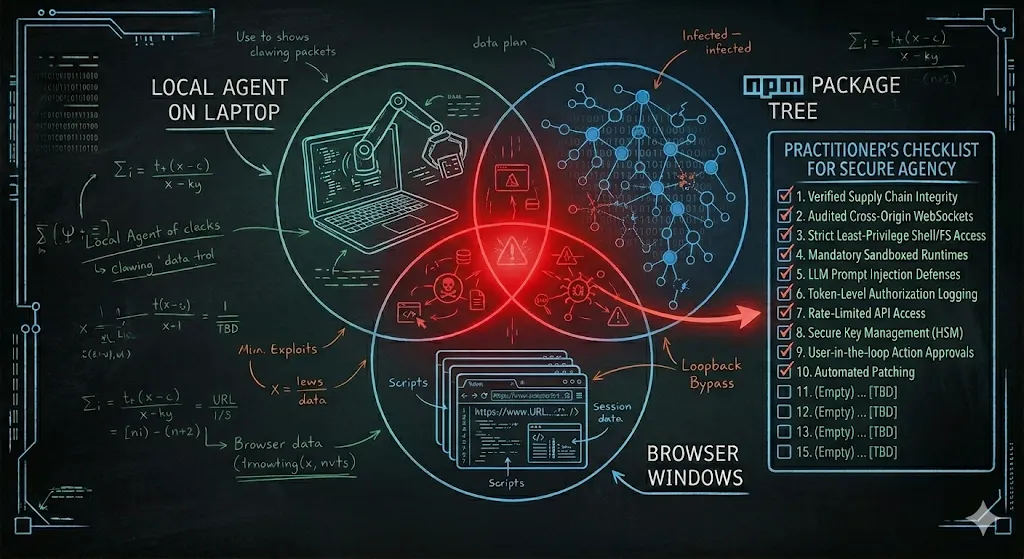
I Want a Personal Agent. I'm Not Running One Yet — Here's What Would Change That
TLDR;
In Part 1 I walked through the March 2026 failures: ClawJacked, the OpenClaw CVE flood, the Axios RAT, the Claude Code source map leak. This post is the constructive follow-up. I’m not anti-agent — I want a personal agent badly enough that I’ve been actively testing alternatives. But I’ve set a bar, and nothing I’ve tried clears it yet. Here’s what the bar looks like, what I’m testing (nanobot, nanoclaw, kubernetes-sigs/agent-sandbox), why prompt injection is the attack you can’t patch with a CVE, and the pre-flight checklist I’d want cleared before I point an agent at my real credentials.

AWS KMS Best Practices: Securing the Secret Ingredients of Your Infrastructure
TL;DR
AWS KMS gives you three flavors of encryption keys — AWS-owned, AWS-managed, and Customer Managed Keys (CMKs). For anything resembling production, CMKs are the only real choice: they give you control over rotation, deletion, cross-account access, and most critically — the ability to kill a key in an emergency. Think of KMS like a hotel’s key management system: the entrance guard has one master card, but the security manager holds the safe with all the master keys. Designing your KMS strategy right is what keeps you from handing that safe to an attacker.
Read More
Kube Security Shifting left, with Armo Security
- Haggai Philip Zagury (hagzag)
- Development , Developer experience ( dev ex) , Presentations , Kubernetes , Youtube , Production readiness , Security
As kubernetes matures into the standard de facto Operating System of the Cloud, in addition to a shift in deployment methods such as GitOps and Continuous delivery paradigms - automation of security is one of our main concerns
Read More